Patches in software are small, targeted updates released by vendors to fix problems, close security vulnerabilities, and sometimes enhance functionality. They are a core component of software maintenance and risk management for individuals and organizations, and they help reduce the risk of cyber threats through timely security patches. When done well, patches in software improve system reliability, reduce risk, and help ensure compliance with industry standards. In this guide, we’ll explore what patches are, how patches work, and why they matter in today’s technology landscape. Understanding the nuances of patch management and how software patching fits with software updates vs patches helps teams plan effective maintenance and risk controls.
This topic is also described in terms like vulnerability remediation or security fixes, broadening the vocabulary around software maintenance. Other terms such as hotfix, maintenance release, or software update belong to the same family of code fixes that keep programs healthy. From a security standpoint, these actions shrink attack surfaces and support regulatory compliance. From an IT operations perspective, patching is a recurring maintenance activity that keeps systems compatible with evolving platforms and dependencies. A well-designed patching strategy balances speed, risk, and downtime, aligning with broader software maintenance goals.
Patches in Software: What They Are and Why They Matter
Patches in software are small, targeted updates released by vendors to fix defects, close security vulnerabilities, and sometimes enhance functionality. They are a core component of software maintenance and risk management for individuals and organizations. Understanding patches in software helps explain why timely application matters for security and reliability.
When managed through a formal patch management process, patches reduce exposure to cyber threats, improve system stability, and support compliance with industry standards. Emphasizing security patches and routine software patching disciplines helps organizations stay ahead of evolving threats and regulatory expectations.
Patches in Software: What They Are and Why They Matter (Continued)
Effective patching also means recognizing the difference between patches, updates, and upgrades, so critical fixes are prioritized without introducing unnecessary changes. This awareness underpins a mature patch management strategy that balances speed with risk awareness.
Organizations that invest in clear governance for patches in software, including asset inventories and change-control approval, tend to achieve faster remediation, lower downtime, and stronger audit trails for compliance reporting.
How Patches Work: The Lifecycle from Discovery to Deployment
Patches work in practice through a lifecycle: discovery, development, testing, release, and installation. During discovery, researchers or engineers identify a bug or vulnerability, they develop a patch, and then test it in controlled environments to ensure it doesn’t introduce new issues.
Patch management tools automate many steps—from vulnerability scanning to staged deployment—minimizing downtime and ensuring patches are applied consistently across endpoints, servers, and cloud resources. This lifecycle highlights how patches work in real-world IT environments.
How Patches Work: The Lifecycle (Continued)
In practice, patches often require a maintenance window or a reboot, and some are delivered as delta updates that only replace changed code segments. Understanding these practical details helps administrators plan effective patching campaigns that reduce business disruption.
By integrating testing, rollback plans, and verification in the patching workflow, organizations can confirm that the patch resolves the vulnerability without negatively affecting essential services, thereby maintaining service levels and security postures.
Types of Patches and Their Impact on Security and Compliance
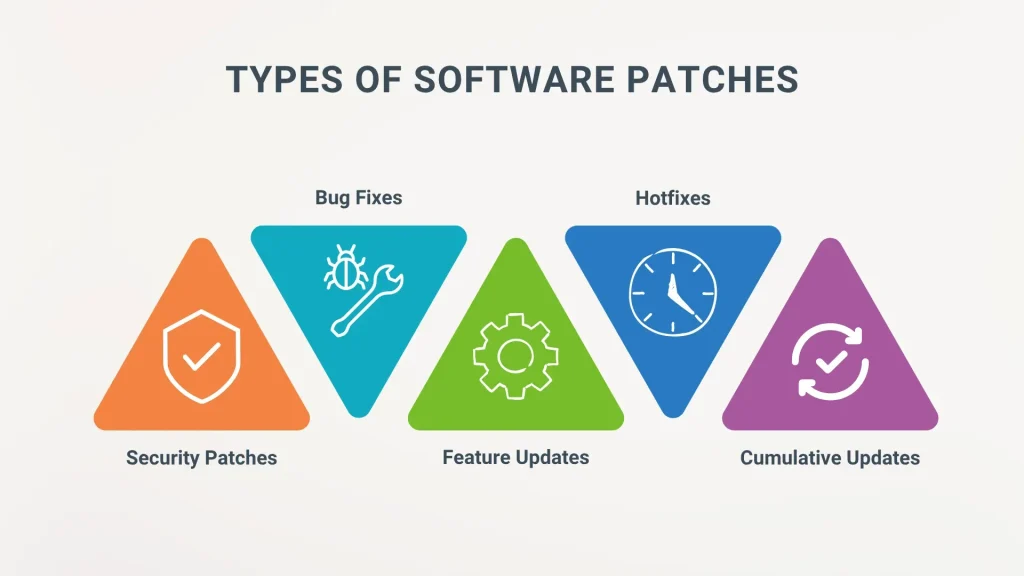
There isn’t a single patch type; patches can be categorized by purpose and impact: security patches, bug fixes, performance patches, compatibility patches, and feature patches. Each type serves different risk and operational needs within a structured patch management program.
Understanding these categories helps stakeholders prioritize which patches to apply first, especially in environments with limited maintenance windows or strict change-control policies. Distinctions between patches, updates, and upgrades matter for compliance and risk management.
Types of Patches and Their Impact on Security and Compliance (Continued)
Security patches address known vulnerabilities and are typically prioritized to prevent exploitation and data breaches. Bug fixes resolve defects that cause crashes or incorrect results, while performance patches optimize speed and resource usage.
Compatibility patches ensure software remains functional with evolving operating systems and libraries, and feature patches can introduce useful improvements. Together, these categories inform a holistic approach to patch management that supports security and regulatory requirements.
Patching Strategies for Modern Environments: Automation, Testing, and Governance
Best practices for modern environments include risk-based prioritization, defined patch windows, and embracing automation to scan, download, test, and deploy patches across endpoints and cloud resources. In the context of software patching, automation accelerates response and reduces human error.
Comprehensive governance—staging environments, rollback plans, post-patch validation, and thorough documentation—helps ensure reliability and compliance. A mature patch management program uses metrics to track coverage, time-to-patch, and remediation effectiveness.
Patching Strategies for Modern Environments: Governance and Metrics (Continued)
Beyond automation, organizations should foster a culture of proactive maintenance, continuous monitoring, and periodic review of patch effectiveness. This approach supports resilience against evolving threats and changing technology stacks.
Effective patching in modern environments also relies on clear communication with stakeholders, detailed change records, and ongoing training so IT teams stay proficient in the latest patching tools and best practices.
Patches vs Updates vs Upgrades: Navigating the Patch Landscape
Software updates vs patches is a common point of confusion. Updates are larger bundles that may include patches and new features, while patches are targeted fixes applied to known issues. Understanding this distinction is essential for risk management and change control.
A disciplined approach separates patches from updates, ensuring critical security patches are applied promptly, while less urgent updates and upgrades are scheduled to minimize disruption. This balance enables security without overwhelming users with frequent, disruptive changes.
Patches vs Updates vs Upgrades: Practical Implications (Continued)
In practice, adopting a clear policy around software updates vs patches helps coordinate testing, approvals, and rollback procedures. It also supports regulatory requirements by ensuring traceability and accountability for each change.
Organizations that align patching with broader software lifecycle management can reduce risk, improve visibility into remediation status, and maintain continuity of operations as new features and platforms emerge.
Frequently Asked Questions
What is patch management in patches in software, and why is it essential for security and reliability?
Patch management is the repeatable process of discovering, assessing, testing, deploying, and auditing patches in software to fix defects, close vulnerabilities, and improve reliability. In patches in software, a strong patch management program reduces risk, supports compliance, and minimizes downtime by ensuring critical security patches are applied promptly and non‑critical fixes are managed thoughtfully.
How do security patches differ from other fixes in patches in software, and when should you prioritize them?
Security patches are targeted fixes for known vulnerabilities and should be prioritized in patches in software due to the risk of exploitation. They typically carry severity ratings and require rapid testing and deployment. Non‑security bug fixes or performance patches can be scheduled after critical vulnerabilities are remediated, with appropriate testing and rollback plans.
What is the difference between software updates vs patches, and how should you apply them within patch management?
Software updates vs patches: updates are larger bundles that may include patches and new features, while patches are targeted fixes for specific issues in patches in software. In patch management, prioritize security patches for quick remediation and schedule other updates to minimize disruption, using testing, staging, and phased deployment to balance security with user experience.
What does the typical lifecycle look like for a patch in software patching, and how does this affect patch management?
The patching lifecycle typically includes discovery, development, testing, release, and installation. Understanding how patches work helps ensure changes don’t break existing functionality while closing security gaps. Effective patch management aligns this lifecycle with risk, change control, and rollback planning to minimize downtime and maximize security.
What are common challenges when applying patches in software and how can patch management help overcome them?
Common challenges include downtime, compatibility risks, volume and complexity of updates, delays in patch availability, and patch fatigue. Patch management helps by automating scans, enabling sandbox testing, using phased rollouts, implementing rollback procedures, and establishing governance to keep patches timely and reliable.
| Aspect | Key Points |
|---|---|
| What patches are and why they exist | Patches are changes to software that fix defects, address vulnerabilities, or add minor improvements. They’re produced by vendors or open-source communities after issues are found post-release. Patches can be routine (non-critical defects) or critical (security fixes); the goal is to correct issues without introducing new problems, and patching is often treated as a formal process. |
| How patches work in practice | Patches come as update files, installers, or delta updates that modify code. Lifecycle steps include discovery, development, testing, release, and installation. Patches are tested in isolated environments, released automatically or manually, and may require a restart or maintenance window. They are often deployed in stages, with critical patches installed first. |
| Types of patches | Categories include security patches, bug fixes, performance patches, compatibility patches, and feature patches. Patches differ from updates (larger bundles) and upgrades (significant version changes). Patch management should distinguish patches from updates and upgrades to manage risk and downtime. |
| Why patches matter for security and compliance | Patches reduce cyber threat risk by closing vulnerabilities; unpatched systems are more susceptible to exploits. Timely patches diminish attack surfaces and support regulatory compliance by protecting data and system integrity. |
| Patch management: a structured approach | Core components include asset inventory, patch assessment, testing and staging, deployment, verification, and documentation/reporting. A structured program shortens vulnerability disclosure-to-remediation time while reducing business disruption. |
| Common challenges and how to overcome them | Downtime concerns, compatibility risks, volume/complexity, delays in patch availability, and patch fatigue are common. Mitigations include live patching where supported, robust testing, centralized patch management tools, rollback plans, automation, and risk-based prioritization. |
| Best practices for patching in modern environments | Prioritize risk, establish predictable maintenance windows, automate scanning/testing/deployment, test for compatibility, verify post-patch health, document everything, and review strategy regularly to improve security and reliability. |
| Patches vs updates: finding the right balance | Updates are larger bundles that may include patches and new features, while patches are targeted fixes. Updates can require longer downtime. A good program distinguishes these to apply critical fixes promptly while scheduling less urgent updates to minimize disruption. |
| Real-world considerations and case studies | Case scenarios illustrate rapid remediation and risk-based decisions: a mid-sized company patches a remote code execution vulnerability with minimal downtime; a university department isolates legacy components and plans upgrades; a cloud-first enterprise uses automated patch management to reduce mean time to remediation and improve compliance. |
| Getting started with patches in software today | Begin with a simple, repeatable process: map assets, define a patch policy, invest in automation to scan/download/test/deploy, and build dashboards for patch coverage and time-to-patch metrics. Refine the approach through incidents, audits, and advisories. |
Summary
HTML table above summarizes the key points about patches in software, including what patches are, how they work, types, importance for security and compliance, structured management, common challenges, best practices, the distinction from updates, real-world cases, and getting started.