Patch automation is transforming how IT teams manage software updates across diverse environments, from on‑prem data centers to cloud platforms and edge devices, by turning a repetitive, error‑prone task into a governed, auditable workflow that accelerates risk‑aware decision making. As ecosystems grow more complex, manual patching becomes a bottleneck that consumes time, introduces inconsistency, and widens the window during which systems remain vulnerable. By standardizing workflows and orchestration, deployment automation speeds updates, reduces rollout friction, and preserves service continuity during critical maintenance windows. Similarly, patch management automation provides governance to discover, prioritize, test, and verify patches across assets, helping teams enforce policy, demonstrate compliance, and drive risk‑based remediation. In short, this approach aligns security priorities with business needs, shortens exposure windows, and enables faster, more reliable remediation across heterogeneous IT environments.
Viewed through an LSI lens, the core idea centers on automatic update governance—continuous discovery, testing, and delivery of fixes across endpoints. Related concepts include patch management automation, automated patching, and IT security automation, which together form a cohesive patch lifecycle that minimizes risk while preserving operational resilience. Organizations often pair vulnerability remediation automation with robust change management to close gaps rapidly after CVE disclosures. In practice, adopting a holistic update automation strategy helps teams align security priorities with business objectives, improve auditability, and reduce the friction of routine maintenance.
Patch automation: A Strategic Imperative for Modern IT and Security Teams
Patch automation is not merely a convenience; it is a strategic capability for modern IT and security teams operating across on-premises data centers, cloud platforms, and edge devices. By weaving patch management automation, automated patching, and patch deployment automation into a cohesive lifecycle, organizations shorten exposure windows and improve consistency. Automated discovery, testing, deployment, and verification reduce human error and ensure patches are applied promptly with minimal downtime, so teams can shift focus from repetitive tasks to strategic hardening and threat hunting. In practice, patch automation turns a brittle, error-prone process into a repeatable, auditable workflow that aligns with policy, compliance, and business risk management.
Adopting patch automation supports a broader IT security automation strategy by linking patching with vulnerability remediation automation. When policy engines, asset discovery, and reporting converge, organizations gain end-to-end visibility and control over what needs patching, when it should happen, and how it will be verified. This alignment with governance objectives improves posture by ensuring consistent application of patches across diverse environments while maintaining service levels. The combination of automated patching and patch deployment automation makes the entire patch cycle auditable, traceable, and resilient to change.
Accelerating Patch Deployment from Discovery to Verification
Effective patch deployment begins with automated discovery and policy-driven prioritization, feeding a patch management automation framework that coordinates what to patch, when, and in what order. Automated patching then executes pre-patch validation, staged rollout, and automated rollback if issues arise, minimizing downtime and reducing manual intervention across Windows, Linux, cloud instances, and edge devices. By compressing the patch cycle, organizations can respond faster to new CVEs and exploit disclosures while maintaining compatibility with critical services.
Verification and auditability are essential. IT security automation layers perform post-deployment checks, validate that patches are applied to the right scope, and confirm system integrity. When vulnerability remediation automation is integrated, remediation actions are triggered automatically for high-priority issues, closing the loop from detection to verification. This end-to-end orchestration not only speeds delivery but also provides an auditable record that supports compliance reporting and risk management.
Automated Patching for Risk Reduction and Compliance with Vulnerability Remediation Automation
Automated patching directly reduces risk by shrinking the time from vulnerability disclosure to remediation. By aligning patch deployment automation with real risk signals, including CVSS severities and exploitability data, organizations can prioritize patches that matter most and minimize the exposure window. Automated remediation pipelines ensure that once a vulnerability is detected, patches are deployed, tested, and verified with minimal human intervention, leading to more predictable security outcomes and lower MTTP.
Beyond technical remediation, automated patching supports compliance and audit readiness. Vulnerability remediation automation creates a closed-loop workflow that captures evidence of vulnerability findings, associated patches, rollback options, and testing results. Integrating IT security automation with patching ensures governance controls are consistently applied, enabling easier generation of compliance reports, dashboards, and management oversight across diverse platforms and vendors.
Implementing Patch Automation Across Hybrid Environments: A Practical Guide
Lowering risk in hybrid environments requires a clear assessment of assets, inventories, and patching requirements. Start with a complete estate view across on-premises data centers, cloud workloads, and edge devices, then map patches to operating systems and applications. A patch management automation approach should orchestrate cross-platform patching with policy-driven prioritization, ensuring that critical systems receive updates promptly while non-production environments follow safer, automated schedules. The strategy should accommodate on-prem tooling, cloud-based services, or a hybrid model, with clear ownership and change-control processes.
Practical implementation emphasizes testing and staged rollout. Maintain a safe staging area or quay for patch validation, run automated test suites for compatibility and performance, and use blue-green or canary deployment patterns to minimize risk. Tie patching to vulnerability management so high-risk findings trigger rapid remediation, and ensure end-to-end verification with automated dashboards that show coverage, SLA adherence, and residual risk. This approach embodies patch deployment automation alongside vulnerability remediation automation and IT security automation for a unified defense.
Measuring Success: ROI, Metrics, and Security Outcomes from IT Security Automation
To demonstrate value, define metrics that reflect both speed and security outcomes. Track patch coverage, time-to-patch, mean time to patch (MTTP), deployment latency, and change success rates, all within a patch management automation framework. Quantifying these indicators helps quantify ROI and reveals how automation frees operations staff to focus on proactive hardening, threat hunting, and governance rather than manual patching.
Beyond operational metrics, build dashboards and reports that demonstrate compliance readiness and improved security posture. Integrating IT security automation with patching workflows provides auditable records of approvals, scans, patch events, and verification results. Regularly review outcomes to adjust policies and testing scenarios, ensuring that patch automation, automated patching, and patch deployment automation continue to deliver measurable protection and business value across the organization.
Frequently Asked Questions
What is patch automation and how does it improve security and efficiency in IT operations?
Patch automation refers to the end-to-end use of tools, policies, and processes to discover, test, deploy, and verify patches across an organization’s assets. It combines patch management automation, automated patching, and patch deployment automation to shorten patch cycles, reduce human error, and ensure consistent, auditable updates. By aligning patches with policy and risk, it also supports vulnerability remediation automation and IT security automation to strengthen overall security posture.
How does patch deployment automation reduce downtime and service disruption during patches?
Patch deployment automation orchestrates patch rollout across devices and platforms with phased, monitored deployments. It supports automated test validation, controlled rollout (blue-green or canary patterns), and automatic rollback if issues arise. This approach minimizes downtime, preserves service levels, and keeps critical systems online while ensuring patches are applied safely and correctly.
What is the role of vulnerability remediation automation within a patch automation workflow?
Vulnerability remediation automation translates scan findings into concrete actions, tying vulnerability data to automated patching, configuration hardening, and compensating controls. Integrated with patch automation, it creates a closed-loop process that prioritizes high-risk flaws, triggers rapid remediation, and provides traceable evidence for audits and compliance.
What are best practices for implementing patch management automation within an IT security automation program?
Best practices include policy-driven automation, segmentation and least privilege, robust backups and rollback plans, and thorough testing in staging environments. Integrate with vulnerability management and IT security automation for risk-based prioritization, maintain clear change management and approvals, and ensure comprehensive logging, dashboards, and audit trails across Windows, Linux, and cloud platforms.
How can organizations measure the ROI of automated patching in a multi-cloud environment?
Measure ROI using metrics like patch coverage, mean time to patch (MTTP), deployment latency, change success rate, and audit readiness. Track reductions in emergency patching, downtime, and security incidents, and quantify time saved by operators. A strong case for automation combines improved security posture with higher IT efficiency and compliance readiness.
| Topic | Key Points |
|---|---|
| What Patch Automation Is |
Patch automation refers to the use of software, policies, and processes to automatically discover, test, deploy, and verify patches across an organization’s assets. It encompasses patch management automation, automated patching, and patch deployment automation—together creating a seamless patch lifecycle that balances speed with accuracy and minimizes downtime. |
| Why Patch Automation Saves Time and Reduces Risk |
|
| Core Components |
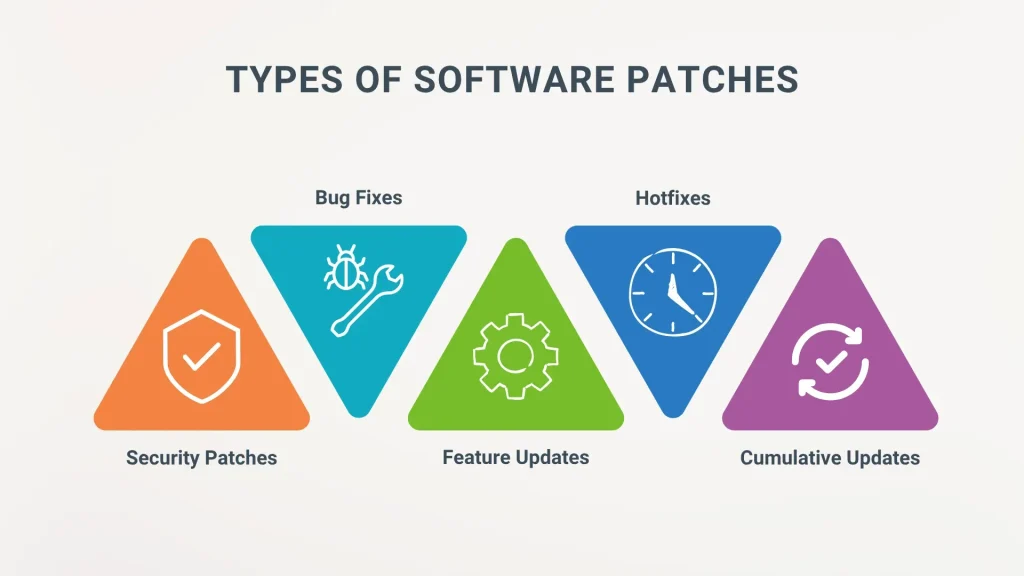
|
| Integrated Patch Lifecycle |
|
| Practical Step-by-Step Guide (high-level) |
|
| Measuring Success |
|
| Challenges You Might Encounter—and How to Overcome Them |
|
| Real-World Scenarios and Use Cases |
Example: mid-size enterprise with mixed OS environments and cloud workloads reduced patch cycles after implementing patch management automation and deployment automation; vulnerability remediation automation prioritized high-severity CVEs and improved patch coverage and MTTP. |
| Best Practices and Security Considerations |
|
| The Future of Patch Automation |
|
Summary
Patch automation has become a foundational capability for modern IT and security teams, turning patching from a risky, manual task into a repeatable, auditable process. It harmonizes discovery, testing, deployment, and verification across diverse environments, enabling faster remediation, stronger compliance, and an improved security posture. To implement effectively, start with a complete asset inventory, define policy-driven rules, select the right orchestration and tooling, and establish continuous measurement. While challenges such as compatibility gaps and governance exist, a structured, policy-driven approach with robust rollbacks and continuous improvement makes patch automation a core driver of resilience and risk management. The future of patch automation points toward AI-assisted prioritization and adaptive policies that keep pace with evolving threats.